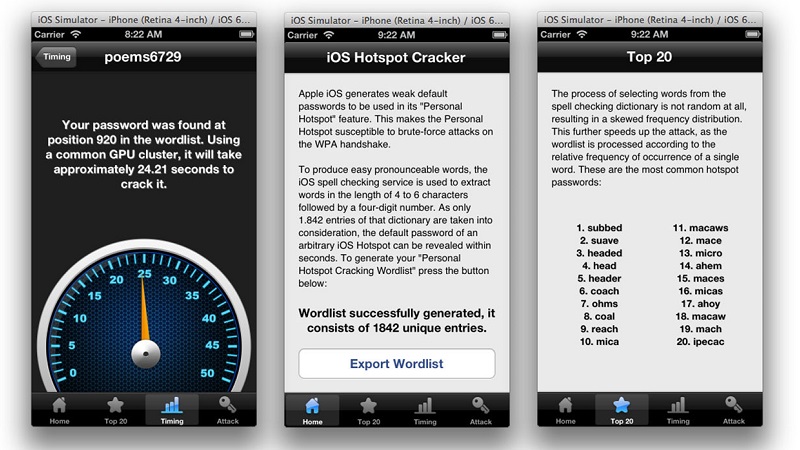
Researchers at the University of Erlangen in Germany managed to crack the automatically generated pre-shared keys used in Apple’s iOS hotspots in under a minute through a flaw in the way the passwords are generated by iOS. The passwords are generated by taking a short 4-6 letter long dictionary word from a list of around 52 500 words (which originated from an open-source Scrabble crossword game) and followed by a series of 4 randomly generated numbers; a process that can only yield around 18 million possible combinations. Upon further investigation the researchers found that only 1842 of the words from the initial list were ever used and to add even more gloom to the equation certain words were used with far more regularity than others. With the power of 4 AMD Radeon HD7970s GPUs the researchers could crack the passwords in around 50 seconds with a 100% success rate. Once the connection is established the attacker can either use your data connection for themselves or potentially use it as a springboard to further attack your device.
In terms of mobile hotspot protection Apple isn’t all that bad, Windows Phone 8 for instance uses an 8-digit number with no other characters which is even easier to crack by brute force attack than the iOS password. The randomly generated passwords are in place so that even if a user doesn’t select a password when creating the hotspot their device will automatically have some form of protection. The safest way to secure your mobile hotspot on your device would be to create your own password with a combination of characters including letters and numbers which would immediately improve the security of any platform’s automatic password generator.
Image source: imore.com