You know that bit in Ocean’s Eleven when Eddie Jemison dresses up as a janitor and sneaks into the Bellagio casino’s server room to hack into the security video feed? That’s pretty much how our office got taken down in real life a couple of weeks ago. And boy, don’t we feel like bunch of kippies for it.
A guy dressed as a telecoms engineer walked right in to an office full of people just after lunch on a Tuesday afternoon, sat down at my desk – opposite another member of staff – and proceeded to strip my hard drive of precious information. He then downloaded sensitive files on to a memory stick, stood up, said goodbye to everyone and walked back to his car.
Of course, he fiddled with a few wires down by the ADSL modem first and mentioned something about a network upgrade, but once he was in the building no-one thought to question him or ask for official ID.
I was not pleased.
To make things worse, my laptop runs a relatively secure operating system – Ubuntu Linux – and has an encrypted hard drive. If only I hadn’t changed my log-in password to ‘Password1’ that very morning. The agony of hindsight.
The hacker was undisturbed for long enough to discover that my laptop wouldn’t read his USB key, so he had to restart the machine from a boot drive, decrypt my hard disk and copy the files he was after over.
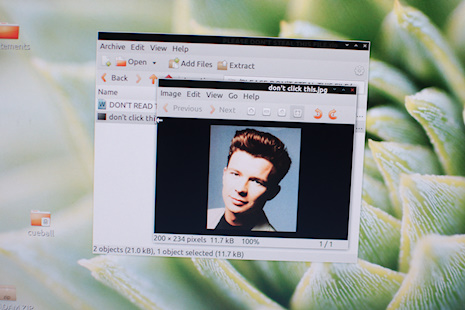
He could have got direct access to our work servers from my machine, and he might even have been able to break into my bank account had he installed a keylogger on his way out. Instead, he got into the very folder which I didn’t want anyone to steal. This one:
And got away with it.
Fortunately – and as you might have guessed by now – the fact that someone walked into our office and hacked into our work network in the most trivial and barely believable manner possible wasn’t a major problem for Hypertext, our parent company. Rather, it was a proof-of-concept attack by Phillip Pieterse, a Senior Security Consultant at the Pretoria offices of SpiderLabs.
SpiderLabs is the research arm of Trustwave, a global security specialist, which works to test networks for PCI compliance and weaknesses against network-based attacks and intrusions. Over in the US, SpiderLabs has been pioneering ‘physical penetration testing’ to augment their online based tests. At Defcon 19 two years ago, Trustwave’s Wendel G Henrique gave a demonstration of how useful this was for assessing a company’s security, right down to manufacturing problems by attacking a VPN, then posing as the engineers who turned up to fix it. The section on giant spiders is especially worth watching.
When Pieterse told me he was planning to bring the same service to South Africa, I laid down a challenge. Get something off of my laptop without alerting any of my colleagues, and I’ll write it up for the site.
Watching him at work really was a little like seeing a movie in real-life – halfway between Mission: Impossible and Inspector Cleuseau. At one point during the preparation, he seriously suggested wearing fake glasses and a moustache. I advised against it, thinking the disguise would be too obvious – now I think he could have pulled it off.
This particular disguise, he said, cost him about R70 for a cap and T-shirt with the logo of a telecoms company embroidered on them. Pieterse’s repertoire as an undercover agent is much more comprehensive than that, though.
“You could pretend to be a networking tech there to fix VOIP phones,” says Pieterse, “As you’d then have access to the telecom rooms and be able to tap phones. You could be pretend to be a building inspector, with a second attacker pretending to be the building manager. This might give un-questioned access to any room in the building. Server rooms, workstations, all kinds of things”
That’s just the basic stuff, says Pieterse. A determined hacker could easily put a building under surveillance and work from there.
“An attacker who has done their research could watch for Janitorial staff,” he says, “And come in as an “employee” while the doors are unlocked. Janitorial staff is very unlikely to questions anybody. Could be somebody their for a real interview, but with malicious intentions.”
The point is, says Pieterse, it’s much easier than you’d think.
“One of the simplest things for an attacker to do, is simply follow somebody through a door. Once somebody is inside, others often believe they are supposed to be here. It’s amazing how far you can get into a building just by being nice to people.”

After operating successfully overseas for several years, SpiderLabs is looking to offer its physical penetration services over here too. Pieterse admits that it may not take off quickly though.
“Many South African firms are still struggling with the basics of network security,” he says, “It’s going to take time to convince people that this is a problem.”
Pieterse is full of anecdotes about clients who have come to him too late. Like the one where someone sat and ‘worked’ at a desk in an open plan office for two weeks before anyone asked him what his actual job was.
“He just stood up, picked up his laptop and walked out,” smiles Pieterse, “They couldn’t believe it.”
It reminds me of the legendary story about film director Steven Spielberg, who claimed that he got his big break by sneaking away from a Universal Studios tour and setting up shop at an empty desk he found in the production area. Sadly, that story is almost certainly apocryphal – but in real life people can, and do, use the same techniques to break into office networks and steal sensitive data. As with much security data, however, companies are reluctant to admit when they’ve been breached through physical attacks and exact numbers of how common it is are hard to come by.
For our experience, it’s a rap on the knuckles for my colleagues – all of whom claim that in hindsight there was something odd about Pieterse but they didn’t like to say anything – and a surprise payload for SpiderLabs. You see, I had the last laugh. Inside that super top-secret file was this:
Congratulations, Mr Super-Disguise-Mystery-Hacker-Man. You just got rickrolled.