Last week Twitter revealed that it had suffered a breach of its systems.
Rather than lax security on the part of users, the social network highlighted that an employee with what we assume is a high-level of access was social engineered.
We use the term social engineering because it’s the official terminology, but in actuality what happens during a social engineering attack is a con.
While this sort of cybercrime is not new, it warrants talking about given that one of the largest social networks has fallen prey to it.
On Friday afternoon we spoke with managing director of KnowBe4 Africa, Anna Collard. KnowBe4 offers cybersecurity and security awareness training to organisations and as such we felt it pertinent to speak to her about this attack on Twitter.
Why is this important?
While we don’t have insight into the inner workings of Twitter, we would hope that the company requires multi-factor authentication for its employees. If that is indeed the case, one must start to question how the attackers were able to circumvent those protections.
“Either the attackers had to collaborate with the employee or it was a really clever social engineering attack where they not only got the employee to divulge their username and password a one-time password as well,” posits Collard.
Of course it’s unclear how the attackers managed to get into Twitter at this stage but the vectors above are believable, especially considering statements from Twitter and reports from other publications.
So how does one spot a social engineering attack?
The KnowBe4 Africa MD tells us that social engineers are similar to con artists in that they play on emotions and often illicit low-grade fear.
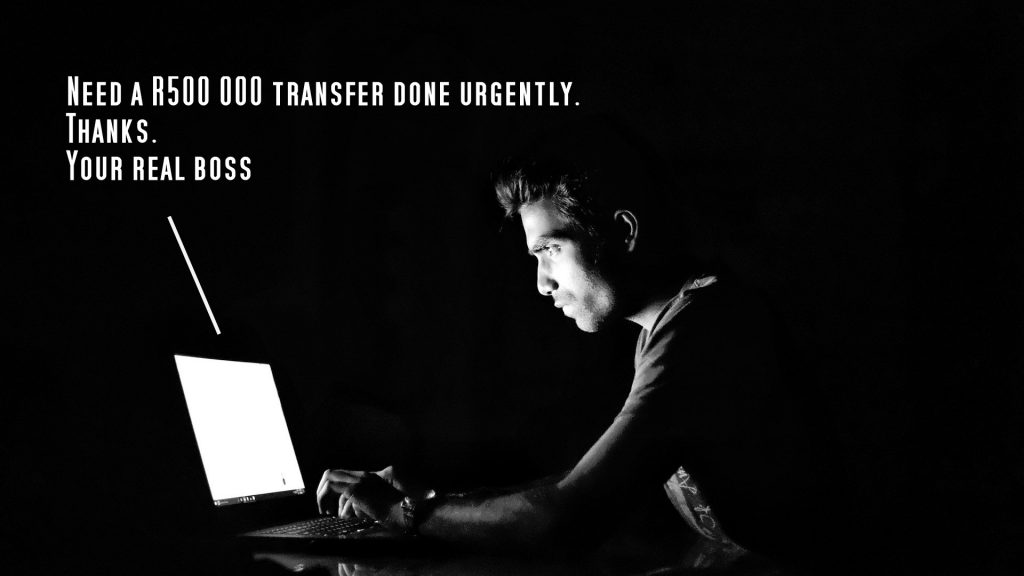
“They try and trigger our emotions so that we don’t think critically about what is happening. It could an email that looks like it came from the CEO saying ‘I need this done urgently. Please jump on it’ and because they are using an authority figure, the target is more likely to act,” says Collard.
Of course an attacker could take a different tack and be flirtatious or flatter the target.
Users are also less likely to question a direction from somebody in a higher position. That is especially dangerous at the moment given the large swathes of people working from home.
It’s for this reason that now more than ever we should be critical of emails from superiors.
Perhaps most alarming is that since the advent of deep fake technology, cybercriminals are able to fake a voice and leave a voicemail. Sure it takes a lot of effort but if you have a big enough target, any investment is worth it in the end.
Social engineering is tough to spot and even cybersecurity professionals will tell you that some techniques are smarter than they would’ve thought possible. Even I have clicked links I shouldn’t have in my many years online.
What is important, especially at a business level is that users know how to address incidents such as this.
“We have a responsibility as an industry to make people aware. In addition to multi-factor authentication and security protection on terminals, you have to inoculate your users to make them aware of these types of attacks because they are ultimately your last line of defence,” explains Collard.
The attack on Twitter has brought home the message that no company is immune to cybercrime.
As Collard concludes, “I don’t think anyone is immune to cybercrime anymore. If you use the internet, you are not immune.”
[Image – CC 0 Pixabay]