When it comes to online scams, anyone who spends any regular time on the internet is wise to most of them.
We all know that we shouldn’t fall for a 419 scam mail that promises us millions of dollars in return for letting a total stranger access our bank accounts, and hopefully we’re learning how not to fall for phishing websites which look like our online bank screen but actually harvest our usernames and passwords for criminal databases.
But how much do you know about “drive-by” malware attacks and how they’re being used today? If it’s as much as the audience at a recent security event in Johannesburg, the answer is probably not enough.
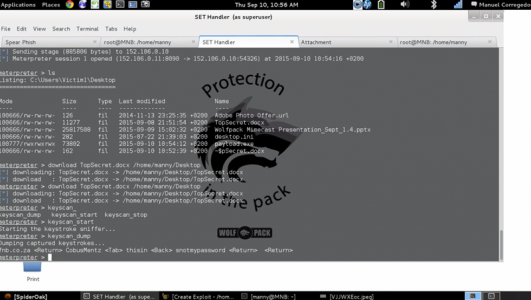
Attendees at the Mimecast Human Firewall conference last week watched agape as Manuel Corregedor, Operations Manager at Wolfpack Information Risk Management, demonstrated how he could fool someone into visiting a website which, with no further action from the user, allowed him to take near full control of their PC in just over 15 minutes.
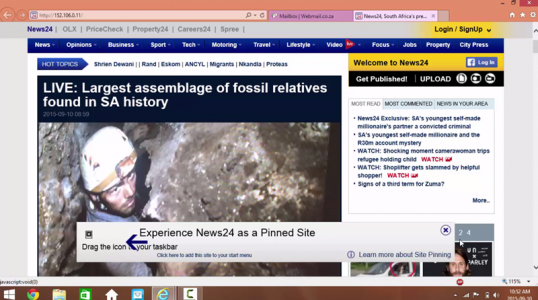
Corregedor used a freely available tool designed for testing corporation’s security policies and user education (which we won’t name here) to successfully clone a South African news website, host it on a notebook and then send a malicious email to an audience member. It took about quarter of an hour to get from nothing to a clicked link.
What happens next was terrifying. In most people’s understanding, the threat of a phishing attack is that a fake bank site will encourage you to enter your login details which can then be captured and stolen by a malicious actor who set it up. Corregedor’s fake site, however, downloaded a small Java exploit to the end user’s laptop – which wasn’t detected by the browser security or the up-to-date anti-virus program running in the background.
This is known as a “drive-by” download, because all you have to do is look at the page and it attacks. By combining a typical social engineering attack and a website loaded with a drive-by download, Corregedor demonstrated what he called “the biggest risk to business today”.
In this instance Corregedor used a Java exploit that has already been patched to deploy the package. He went on to explain that though this vulnerability no longer exists in recent version of Java, it is common practice among organisations that make use of legacy systems to require older versions of Java and force users’ machines to hold off updating. This has the potential to leave backdoors open to attacks like this one which could compromise a company’s entire network.
The payload program that was uploaded to the attacked notebook however, is a zero day vulnerability that has not yet been patched and this could mean other threats are out there waiting to be discovered.
Once the exploit code was active, Corregedor demonstrated that he could log keystrokes from the target’s device, download their documents and even take control of the infected laptop’s web camera. From here, getting access to the corporate network the user is logged into would be a cinch.
The video below is from the presentation. Apologies for the poor audio quality, but in it you can see exactly how long it takes Corregedor to attack a laptop and what he has the power to do with it afterwards.
Corregedor’s email played on the threat of a national blackout – something sure to get a South African’s attention right now. The email explained that the national power provider had announced a nationwide blackout was to be implemented and more information could be found at the accompanying link. To the average user this link appeared innocuous enough but once clicked it redirected the user to the cloned website on Corregedor’s notebook.
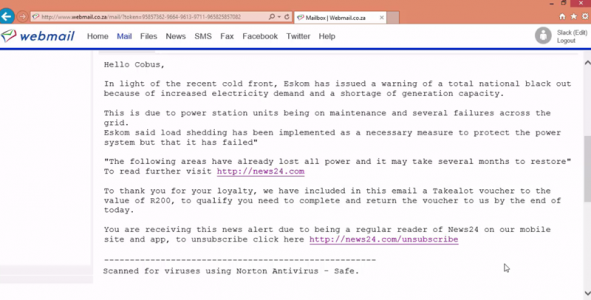
To the well versed internet denizen, several tell tale signs were visible during the hack such as Corregedor’s IP address being where the news website’s URL should be, and no sign of the blackout news mentioned in the email. These signs often go unnoticed by users because they’re too fearful, scared or excited to care about details as “small” as a URL.
Meanwhile, as the user searched for the news of a blackout Corregedor was free to wonder around the user’s computer. Corregedor went on to tell us that even if the user was to close their browser this connection would persist, adding that “if I wanted to I could make it completely persistent which means even if they restarted the machine I would always have access”.
According to Giulio Magni, Senior Sales Engineer at Mimecast, the average time it takes a company to detect a hack of this nature is 297 days.
Social engineering is more commonplace than one would think, and it’s going to get more targetted and more sophisticated. With the recent Ashley Madison hack and accompanying data dump users were left vulnerable to social engineering attacks such as this. With this type of database out in the open, criminals can craft an email that doesn’t just rely on your address and a vague promise of riches, they know your real world address, sexual preferences and a host of other detail that can be used to lure you in. A number of email scanners that marketed themselves as being able to let you know if your email address had been compromised were harvesting emails. An online security company, KnowBe4, also warned their clients about similar attacks happening in the wake of the hack and urged companies to warn users not to submit to threats or click suspicious links.
The best defence against this type of attack, says Magni, is education. With URL phishing scams increasing by 233% in the last year according to Magni, users, whether they are employees or just a person at home, must be more aware of what sort of attacks they are susceptible to in order to be truly secure. You can of course purchase software that scans URLs and documents for malicious content in real time but internet safety starts with a user’s browsing habits he concludes.
[Image CC by 2.0 – Perspecsys Photos]

