ABSA announced yesterday that it’s planning to test out fingerprint authentication for its Visa-based credit cards.
With this news and the fact that South Africa’s national ID Card (which can be applied for at some branches of FNB and Standard Bank) is now being issued with on-card biometrics, it’s looking likely that fingerprint readers are going to start cropping up everywhere very soon for authenticating transactions and proving your identity. And while that’s not necessarily a good thing, we thought it’s time to take a step back and explain how biometrics work for ID verification in these cases.
South Africa’s new national ID card is a clever piece of gear, which the Department of Home Affairs is touting as a way of reducing fraud across the public and private sectors.
The card has a small gold chip on the surface contactless chip underneath the surface which can hold up to 80Kb of encrypted data. It’s not configured for as many uses as the new Nigerian ID, which doubles up as a payment card, but it’ll surprise a lot of you as to how much you can fit into 80Kb. According to the latest figures, there’s around two million smart ID cards currently in circulation.

The first step to getting a card that stores biometric information is to be “enrolled”. You sign up, fill in your forms and during the process your fingerprint is taken.
The accuracy of this can vary a lot – one manufacturer which has just launched a sensor in South Africa, Lumidigm, says that it takes 12 different photos from different angles and with different sensors that penetrate the skin to ensure it’s a real fingerprint. It demos the accuracy of its sensors by inviting journalists to try spoofing them with fake fingers.
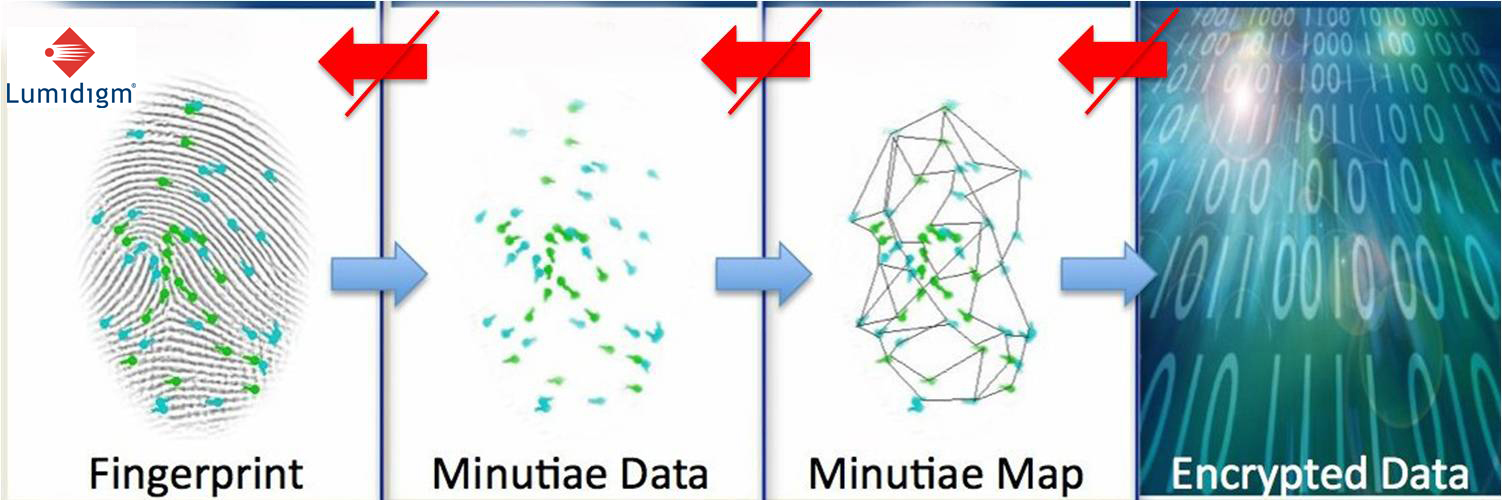
What’s actually stored on the card, though, isn’t a large number of JPGs as these would eat up all the memory in a credit card chip. Instead, it’s a much simplified “template” pattern based on key points in the layout of your fingerprint. This is only a few bytes in size, but almost as unique as the fingerprint itself and internationally recognised as an accurate way of verifying your ID.
This is stored in encrypted format on the chip along with details like your ID number or bank account, name, address and a low-res photo.
When the card is presented as a means of verifying your identity – if you want to pay for something with a biometric credit card, for example, or use a national ID card to take out a cell phone contract without the palaver of RICA documents – it’s placed in a card reader where the stored information is decrypted and read.

Any human operator can then confirm that the photo on the chip matches the photo on the card matches your face, for example, and a fingerprint reader can be used to confirm that your digits match the ones used to enrol the card.
Obviously the weaknesses in the system are around accuracy, but fingerprint readers are getting good in this regard. HID boasts that it’s tackled most of the major problems, like fingerprints getting faint with age or dirt on your hands making prints hard to read.
The other problem is that if anyone gets hold of the right encryption keys, they may be able to copy data off of your card illicitly – or, worse, write new data to the chip. The latter problem engineers should prevent against, but may be an issue in weak systems.
In principle, says HID’s Greg Sarral, using on-card authentication in this way should assuage privacy fears – no data needs to be transmitted anywhere to verify your ID, so there should be no record that an authentication took place.
Of course, actual implementation may differ. Obviously when you pay for something with a biometric Visa card, there’s going to be a record that the transaction took place on your bank’s servers. As far as the national ID card goes, according to the chip manufacturer Gemalto it is designed to be used to authenticate offline, so there won’t have to be a connection to a Home Affairs server in order to check a fingerprint.
Exactly what Home Affairs will require from third parties, however, hasn’t been confirmed yet. According to people we’ve spoken to the priority for the department right now is increasing its capacity to enroll people on the system and opening up APIs or sharing keys with companies that want to use the card is limited to the banks who are also enrolling on DHA’s behalf.
The final problem is one for the future: it’s often said that the weakness with biometric security like fingerprints is that it’s a password you can’t revoke if someone steals it. Today, not all fingerprint sensors are created equal in terms of security and ability to recognise a real fingerprint from a fake. Tomorrow, even the readers that currently appear invulnerable may be cracked. And there’s always the issue that centralised databases like the one at the Department of Home Affairs may be cracked and leaked, along with all that fingerprint template data.
HID’s Sarral says that the key to making biometrics futureproof is by using readers (like HID’s) which test for “liveness” – that a fingerprint is attached to a living finger.
“A biometric template database without liveness information is useless,” he says, “If someone were to hack a template database, they only get the templates. These templates cannot be deciphered to recreate a fingerprint as they are a binary representation of various points of minutia. You still need to have proper liveness detection when using a HID sensor to trigger a match with a template. Therefore, gaining access to a template database only provides half of the equation. To properly validate the liveness threshold must be met.”
Of course, not all sensors have the same level of sophistications for detecting live fingerprints – we’ll have to wait and see what the DHA mandates.
[Main image – CC CPOA]
//This post was updated on 28th Sept. The original stated that the National ID card has a chip on the card’s surface, whereas it’s actually embedded inside the plastic.

