Last week we brought you news that adware targeting M1-powered Macs had been discovered in the wild and this week, well there is more cause for Mac owners to be concerned whether they use the latest iterations or not.
Cybersecurity firm Red Canary last week published a blog post detailing a new strain of malware targeting the macOS operating system. The firm dubbed the malware Silver Sparrow and, it’s an odd one.
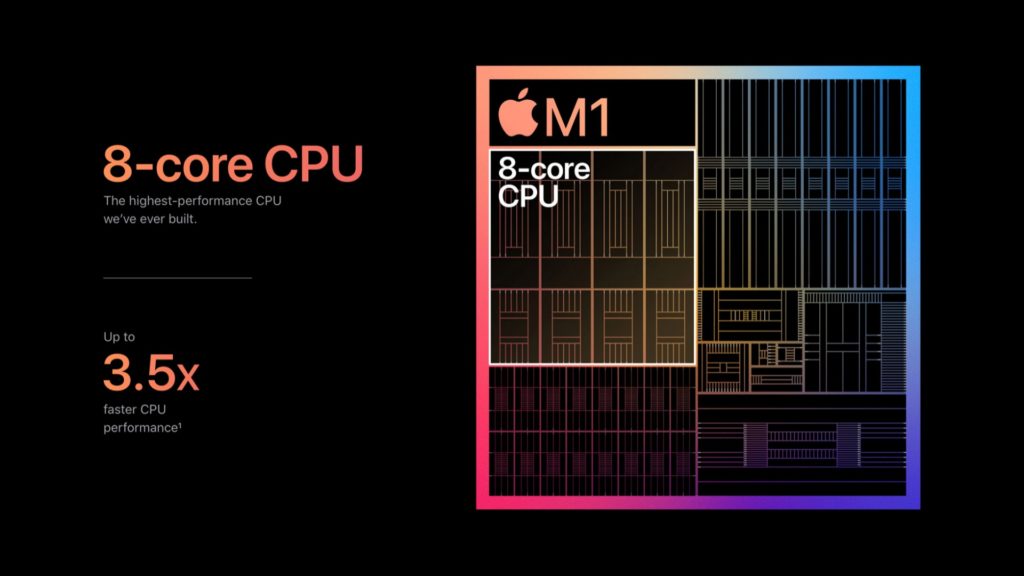
For one, much like the adware we covered last week, this malware contains architecture for Intel x86-64 systems as well a M1 ARM64 systems.
“We’ve found that many macOS threats are distributed through malicious advertisements as single, self-contained installers in PKG or DMG form, masquerading as a legitimate application—such as Adobe Flash Player—or as updates. In this case, however, the adversary distributed the malware in two distinct packages: updater.pkg and update.pkg. Both versions use the same techniques to execute, differing only in the compilation of the bystander binary,” writes Red Canary.
The good news is that Silver Sparrow hasn’t been used to execute any malicious payloads just yet but it is still a reasonable threat according to Red Canary. Apple has also revoked the bystander binary signature so future installations should prove more difficult.
But concerns still worry researchers because Silver Sparrow can be used to deliver a malicious payload and while it hasn’t done that yet, it could.
More concerning is that this malware has been spread to “29,139 macOS endpoints across 153 countries” as of 17th February.
Curiously, the binary packages contain script that would only run if a user sought them out. When run these binaries display the messages “Hello World” on Intel x86-64 systems while “You did it” is displayed on M1 ARM64 systems.
“The purpose of the Mach-O binary included inside the PKG files is also a mystery. Based on the data from script execution, the binary would only run if a victim intentionally sought it out and launched it. The messages we observed of “Hello, World!” or “You did it!” could indicate the threat is under development in a proof-of-concept stage or that the adversary just needed an application bundle to make the package look legitimate,” the firm said.
Red Canary has also outlined what indicators of compromise the malware leaves behind. You can find that information along with a high-level analysis of the malware here.